There is a scenario today that is becoming all too common and it goes something like this:
- Girl on internet meets guy that she doesn’t know
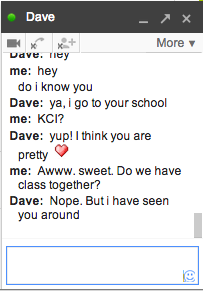
- Guy befriends girl over hours, days or months
- Girl becomes comfortable with guy
- Guy, innocently asks girl to see her nude, PROMISING never to share the image or reassuring the girl that it is a video
- Girl reluctantly obliges
- Guy reveals himself as being someone else and threatens girl or girl’s family if she does not provide more photos or cash (the sextortion)
There are a few things at play here:
Catfishing. This is where a user pretends to be someone else. The term became popular after a 2010 documentary by the same name where a young guy, Nev Schulman, develops a relationship with a young woman in her 20s, only to discover she is actually a married middle-aged woman just looking for a connection. Though in this case the end result was not harmful, it was still hurtful to Nev, who thought he’d fallen for someone else. This type of thing happens often enough in online dating that Nev now has his own Catfish TV show on MTV.
Grooming. A situation where someone uses deliberate tactics to establish a connection with a victim to lower their inhibitions in order to abuse them. Grooming is not specific to the internet but is being used to describe the same process online as in real life.
Either catfishing or grooming can be dangerous and harmful, but together they are quite scary. The most famous case of note is the suicide of Amanda Todd. Prior to her death, Amanda posted a video explaining her situation. At 13, she met a guy online with whom she was chatting on Skype video. He said he liked her. He said she was perfect. He asked her to flash him. She did. He took a screen shot. What followed was months of torment including the public airing of her photo. Eventually she couldn’t handle the ridicule and took her own life.
All these scenarios mention young girls because they have the highest incidence of no reason why this couldn’t also happen to boys, grown women or grown men!
Stranger Danger
There is an old saying that “a Stranger is just a friend you have not met”. It seems incredibly easy to befriend someone online because it takes away all the awkwardness of physical interactions. People feel more free when hidden behind their keyboards. It is easy to think you have ‘met’ a person this way. Not true. The problem is that the person on the other end is STILL a stranger. You don’t actually know anything about them.
For online purposes, ‘stranger’ should be defined as someone you haven’t met OUTSIDE the computer world.
Protecting what’s yours
The way predators get to victims is by getting them to reveal things online that they shouldn’t. Since any digital photo, conversation or email is vulnerable to one day ending up in the wrong hands, you should consider what you are sharing online even with family and friends you know well. At a minimum, protect the following:
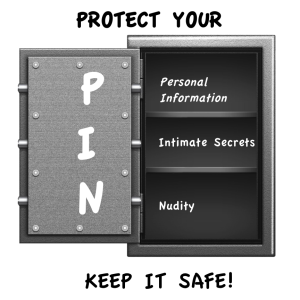 P – Personal Data. Anything that is specific to you: real name, address, school, place of work, family members. There are places you may want to share this kind of thing online but never in a chat with a ‘stranger’. This information is perfect bait to lure you in.
P – Personal Data. Anything that is specific to you: real name, address, school, place of work, family members. There are places you may want to share this kind of thing online but never in a chat with a ‘stranger’. This information is perfect bait to lure you in.
I – Intimate Secrets. The internet is not the place to divulge your deepest, darkest secrets. Things you are insecure about, things you are afraid to tell people. That is the kind of information that will be used against you.
N – Nudity. This one I would stress, not ever. Video has screen capture. There are no ‘safe’ places to store the pictures. Once done, this can never be undone or unseen.

Leave a Reply